Apple’s refusal to comply with a court order to provide the FBI with a backdoor into the iPhone has opened a new chapter in the debate of security vs privacy.
We’re entering a new stage in what is already a heated battle between Apple and the Bureau, one that will set the stage in the war over encryption for years to come.
Here are five things you need to know about Apple’s fight with the FBI.
1. What the FBI wants
Essentially, the FBI wants to crack the passcode on an iPhone 5C used by one of the shooters in the 2015 San Bernardino terrorist attack. The FBI doesn’t have the PIN, and after ten failed attempts, the agency fears the phone will wipe what data is on there – a standard iPhone security feature.
On Tuesday, a judge ordered Apple’s “reasonable technical assistance” to do three things: bypass or disable the auto-erase function on the phone, enable the FBI to electronically input passcodes from another device hooked up to the iPhone and ensure the phone’s software doesn’t impose time delays between passcode attempts beyond what’s incurred by Apple’s hardware.
In other words, the FBI wants to unlock the iPhone by brute force by attempting many, many passcodes until it hits on the right one, without having to manually input them and without a delay after every incorrect attempt.
2. The special version of iOS
To get around the three things listed above, the FBI basically wants Apple to make a special version of iOS for the recovered iPhone.
The court order maintains the software would have an identifier for the phone coded by Apple so that it would only work on that specific device. This special version of iOS would be loaded via Device Firmware Upgrade (DFU) mode, recovery mode or “other applicable mode available to the FBI.”
The FBI needs Apple to make the firmware because, before the update kicks in, the device will verify that it has a valid signature from Apple. If it doesn’t have the signature, then the firmware won’t take.
The court order indicates that this special operating system would be loaded onto the iPhone 5C at a government facility or at an Apple facility. If it takes place at an Apple location, the FBI would have remote access to the device so it could try passcodes on it.
3. What the FBI is asking for is possible
There has been debate about whether what the FBI is asking Apple to do for is even possible, and my research indicates that it would be difficult for Apple to accomplish it on a locked phone running a more recent version of iOS.
However, according to Trail of Bits, what the FBI is asking for is technically possible due largely to the fact that the iPhone it wants to crack is a 5C.
This device doesn’t have what’s called a Secure Enclave, the “single most important security feature produced by Apple,” writes Trail of Bits. The Secure Enclave is a separate coprocessor within the A7 chip, found on iPhones with Touch ID. The iPhone 5C is not one of those iPhones.
When a passcode is entered on an iPhone that has a Secure Enclave, that passcode attempt is “tangled” with a key from the Secure Enclave, and not even Apple knows that key. So even if Apple created a new version of iOS to circumvent the other security features, if the device has a Secure Enclave, it would be virtually impossible to crack.
However, no Secure Enclave means that all you have to contend with is the passcode protections in the software itself, which takes us back to the FBI wanting a special version of iOS in the first place.
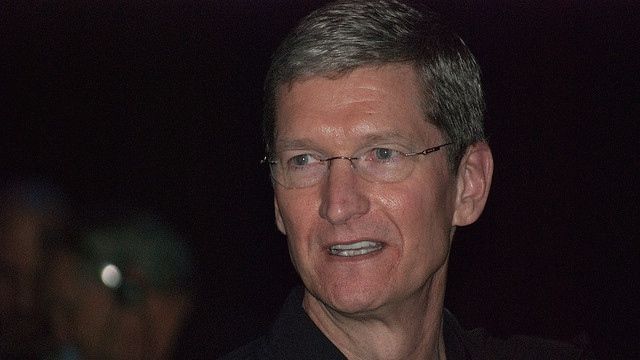
4. Why Tim Cook is refusing to comply with the court order
Cook wrote an open letter to customers lambasting the FBI’s request for Apple to take what he called “an unprecedented step” that would threaten the security of Apple’s customers.
You can read Cook’s letter in full here, but it’s important to point out why he is refusing to comply.
Cook wrote that even though the FBI says it wants to use the special version of iOS on just the one iPhone, the software would “undeniably create a backdoor,” and, like Dr. Frankenstein’s monster, it’d be difficult, if not impossible, to control once it’s made.
“Once created, the technique could be used over and over again, on any number of devices,” Cook wrote in the letter. “In the physical world, it would be the equivalent of a master key, capable of opening hundreds of millions of locks – from restaurants and banks to stores and homes. No reasonable person would find that acceptable.”
While Cook wrote he believes the FBI is acting in good faith, he says the software it’s asking for is “too dangerous to create.”
It also sets a precedent for future demands by the US (or any nation’s) government for Apple (or any tech company) to create backdoors that put customers at a risk for attack, and that’s not something Cook is willing to take the lead on.
5. What the tech world is saying
Several in the tech community have spoken out about Cook’s letter and the situation at large, and most are supportive of Apple’s decision.
Jan Koum, co-founder of WhatsApp, took to to Facebook to laud Cook’s letter and called for resistance to the FBI’s demands.
“We must not allow this dangerous precedent to be set,” Koum wrote. “Today our freedom and our liberty is at stake.”
T-Mobile CEO John Legere was asked on CNBC where he “comes down” on the situation: “[Cook is] in a really, really difficult spot. Obviously what we’ve got is an unheralded situation where he’s being requested to help authorities deal with the security in the device… I wouldn’t know how to advise him, but I understand both sides of the issue. And I think it’s groundbreaking.”
Everyone (including myself) was waiting on a reaction/response from Google, and we finally got one in the form of tweets from CEO Sundar Pichai late Wednesday afternoon.
Pichai sided with Apple, calling Cook’s letter “important” and writing that, “[f]orcing companies to enable hacking could compromise users’ privacy.”
He warned that requiring companies to hack their customers’ devices and data could result in a “troubling precedent,” and that thoughtful and open public discussion should take place over the issue.
Apple plans to appeal the judge’s order by next week, but as the FBI’s options to access the iPhone have seemingly run out, we’re likely to see further public debate between the two entities, privacy and security advocates, and members of the public who, ultimately, have a massive stake in what’s decided.
Image credit: Valery Marchive (LeMagIT)/Wikimedia Commons
Source: techradar.com







































Why not give the phone to Apple, they unlock it, and give it back to the Feds. Seems like Apple is milking this perfectly legal request for increased sales whilst at the dismay of the victims families.
'"Once created, the technique could be used over and over again, on any number of devices," Cook wrote in the letter. "In the physical world, it would be the equivalent of a master key, capable of opening hundreds of millions of locks – from restaurants and banks to stores and homes. No reasonable person would find that acceptable."'
Except it's clear that's not entirely true. As noted here and in many other places, with the 5S and later, this trick isn't possible at all (or at least, would be many, many orders of magnitude more difficult). It's not a backdoor (as a lot of people keep calling it) since it's not something being added to the OS for general distribution. In fact, the FBI is even willing to let Apple hold onto the phone and the patched OS inhouse and destroy it afterwards (and one assumes, restores the original OS to the iPhone in question).
Once created it can be used ONLY with iPhones without the TPM component (the so called 'Secure Enclave' because you know – Apple has problems using the same language anyone else does) and most of those are either out of service or insecure to some degree anyway.
Don't think so? Essentially what's happening here is that the FBI is asking Apple to jailbreak this phone. That's exactly the same process – a modified version of the OS is installed over the standard version using DFU. Heck, I've done this myself (no – I don't know how they do it – I just used the kits out there to jailbreak my old iPhone 3G…)
And the image in question, as noted, would be locked to this specific phone – so even if it got out, it couldn't be used with any other phone. The act of signing it simply makes this all much simpler and safer (in terms of the data on the phone).. and Apple signs every release they make – so again, nothing new. If signing this is dangerous – signing every release is equally dangerous.
So, sorry – from everything I've been able to read about this situation, Cook is trying to make himself out to be acting to protect his loyal customers when that's simply not the reality here.